Halloween is coming up (and so is our Simplify Cybersecurity webinar!) so let’s dive into one of the scariest subjects for any small-to-medium sized business (SMB): cybersecurity threats. Cue the spooky music and blood-curdling scream.
But, in all seriousness, every year cyber trends shift, and new threat vectors emerge and it can be exhausting to keep up! The good news: Your friendly local BP/IT team deals with this every day, so we can give you the unique SMB-specific perspective and what businesses like yours see every day.
In 2025, malicious URLs continue to rapidly grow as one of the primary email threats. URLs have become four times more common than malicious attachments. While they are still common too, if your employees are just focusing on attachments, your company’s at a major risk. Your credentials are more valuable and more versatile than a malicious attachment infecting your network. The bad guys don’t break in anymore, they log in.
So, what does this mean for your business? Your security software and solutions matter, but your people are the primary target. We don’t yet live in the dystopian future where employees get security software installed in their brains yet, so training is the key!
So far in 2025, we’ve seen rapid growth in these four major attack routes:
Telephone Based Attacks
It sounds crazy at first, but what’s old is new again. Bad guys are social engineering purely over the phone, and this makes it difficult to defend with any security software. With AI, the bad guys are often able to pretend to have your bank or multiple other people on the line with you, making it all the more convincing. We’ve seen people give away banking info or other financial information over the phone—or give bad guys keys to the kingdom with passwords over the phone. Without user training and double-checking safeguards in place, there’s very little defense to these.
MFA Immune Phishing
While it’s a huge help, multi-factor authentication (MFA) doesn’t make you invincible, and that’s becoming more and more true this year. We’ve seen a dramatic increase in phishing that steals a valid login session and not just credentials once you’ve logged in to the fake page, meaning they don’t even need to put in a code from your phone to get in. Once that’s done, they can add whatever other login methods or authenticators of their own, guaranteeing persistent access.
This is why the BP/IT team has rolled out Huntress Identity Threat Detection & Response internally and to all of our clients. This has become one of those mandatory security solutions. It detects and acts on suspicious logins and locks the accounts within seconds of seeing suspicious activity. Even the most security-conscious people get caught eventually, and this solution can save a business. Want to learn more? Get a free tech evaluation from our BP/IT experts.
Conversation Hijacking
Email compromise tends to spread like a virus (and we really DO NOT need another pandemic). While random attachments and links are still pretty common because they’re so easy to mass mail, we’ve seen another huge increase year over year in bad guys picking a few random threads from a compromise mailbox to target a few associated companies by replying to them and subtly redirecting the new targets to a mailbox or site that they control. This relies on the trust we have for people we’ve worked with for years and years.
Got a random email from someone you know that seems irrelevant to the email its replying to from a year ago? That’s probably a bad guy starting to lay a trap for you.
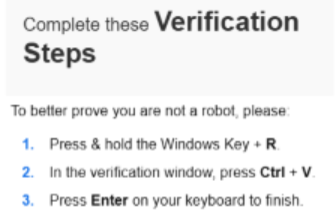
Fake CAPTCHA and Verification Codes
This was called out last year in our webinar and blogs as a brand-new threat that was predicted to become a major force. Spoiler: It has.
It’s deceptively simple. After invisibly loading some text into your clipboard, a site asks you to verify you’re a human by pasting some text in a run box. It just looks like it has pasted a gibberish set of letters like any multi-factor code, but it’s actually running an encrypted malicious script that will download a backdoor and malware onto your machine. We’ve been able to catch these with Huntress, but so many people are just used to doing whatever a site says to prove they’re not a robot.
What’s A Small Business To Do?
Invest in training your team. Phishing testing and video training is important. Creating a culture of collaboration and openness is crucial. If your team feels like they’ll be blamed for falling for something, they may sweep it under the rug. However, if you reward your team for catching a sophisticated attempt, they’ll look out for your business and each other.
Not sure where to start with your cybersecurity plan? We’re here to help. You can download our FREE Cybersecurity Checklist to see where you stand or, even better, book a free tech consultation today. We’ll take a fresh look at your current setup, walk through what’s working (and what isn’t), and answer your questions without any pressure or jargon. Just clear advice from your local team that cares.